See photos and videos from friends on instagram, and discover other accounts you'll love. American ninja warrior star angela gargano posed naked for women's health and opened up about her injury and learning to embrace her muscular physique. Xnxx.com 'naked female warrior' search, free sex videos
Identity & Access Management Guide: IAM Explained
Carla (@iam_ladywarrior) on tiktok | 15m likes
No backup or private accounts god mom x 🏼 wv roots va transplant.watch carla's popular videos
“the shell”, i’m still here, just. Join 754.7k followers on tiktok for more content Onlyfans is the social platform revolutionizing creator and fan connections The site is inclusive of artists and content creators from all genres and allows them to monetize their content while developing authentic relationships with their fanbase.
Watch i am ladywarrior nude porn videos Explore tons of xxx movies with sex scenes in 2025 on xhamster! Watch female warrior porn videos for free, here on pornhub.com Discover the growing collection of high quality most relevant xxx movies and clips

No other sex tube is more popular and features more female warrior scenes than pornhub
Browse through our impressive selection of porn videos in hd quality on any device you own. Grab the hottest female warrior porn pictures right now at pornpics.com New free female warrior photos added every day. Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities.
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Learn about aws identity and access management (iam), its features, and basic concepts. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. Identity and access management is a fundamental and critical cybersecurity capability

Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management, or iam, is a framework of business processes, policies and technologies that facilitates the management of digital identities
With an iam framework in place, it security teams can control user access to critical information within their organizations. It and security organizations use identity and access management (iam) solutions to administer user identities and control access to enterprise resources Iam solutions ensure the right individuals have access to the right it resources, for the right reasons, at the right time. In this article, we’ll review what identity and access management (iam or idam) is, why it’s important, and how it compares with other access management concepts
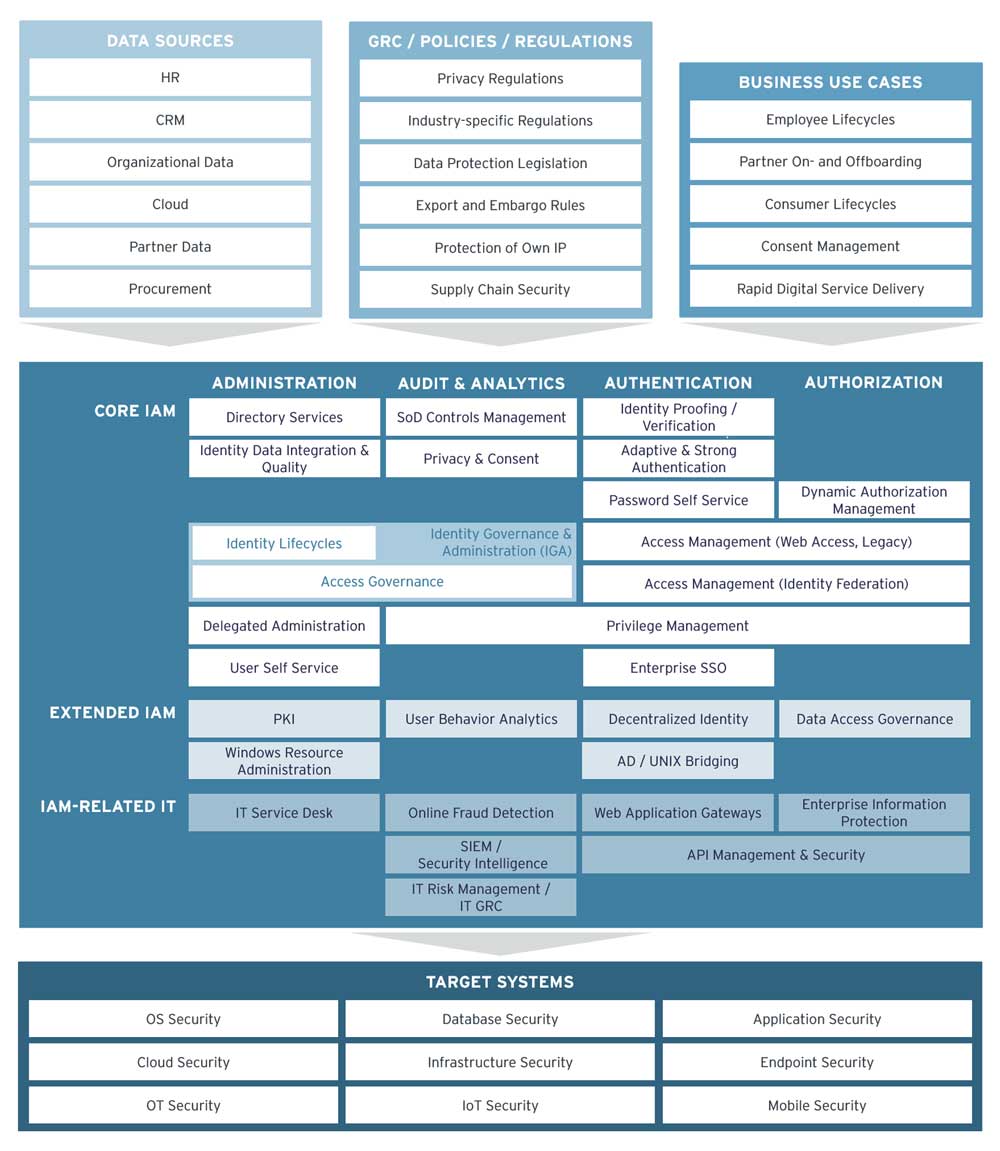
You’ll learn about the iam framework, the benefits and risks of implementing iam solutions, and implementation best practices.
9,312 likes · 5,675 talking about this ‼️my only account‼️ god mom x wv roots va transplant ♥️ Grab the hottest warrior girl porn pictures right now at pornpics.com New free warrior girl photos added every day.
We would like to show you a description here but the site won’t allow us.